Home
/ Blog /
A Primer on HIPAA ComplianceA Primer on HIPAA Compliance
February 13, 20248 min read
Share
In today's digital age, where personal information is constantly exchanged and stored online, the security and confidentiality of health data have never been more critical. This health data could include your medical reports, transcripts, insurance details, and more. The Health Insurance Portability and Accountability Act (HIPAA), enacted in 1996, transformed how healthcare handles sensitive data. Born out of the shift from paper to electronic records, HIPAA addresses the host of new challenges and vulnerabilities - like data breaches and unauthorized access, that come with the digital transformation of the healthcare system. And all of this is to safeguard personal health information.
Despite being a federal law, HIPAA's interpretation and implementation vary among organizations, adding complexity due to the diverse ways electronic Protected Health Information (ePHI) is created, transmitted, transformed, or stored in tech products and services.
In this blog, we will give a primer on what HIPAA compliance is, who it applies to, what are the key guiding principles, and how it applies to the new age tech companies.
Who does it apply to?
Department of Health and Human Services (Referred to as HHS henceforth) has explained HIPAA’s scope quite succinctly but broadly.
Covered Entities
Organizations or individuals offering health plans, healthcare providers (doctors, clinics, pharmacies, etc), and healthcare clearing houses. These are the primary entities responsible for maintaining and protecting PHI under HIPAA.
Business Associates
A business associate is a person or an entity that performs certain functions or activities involving the use or disclosure of PHI on behalf of, or provides services to, a covered entity.
Subcontractors
These are third-party entities that business associates engage with to carry out some of their services. A subcontractor is a business associate of a business associate and must comply with the same HIPAA requirements.
The following diagram depicts the relationship between the different entities along with an example.
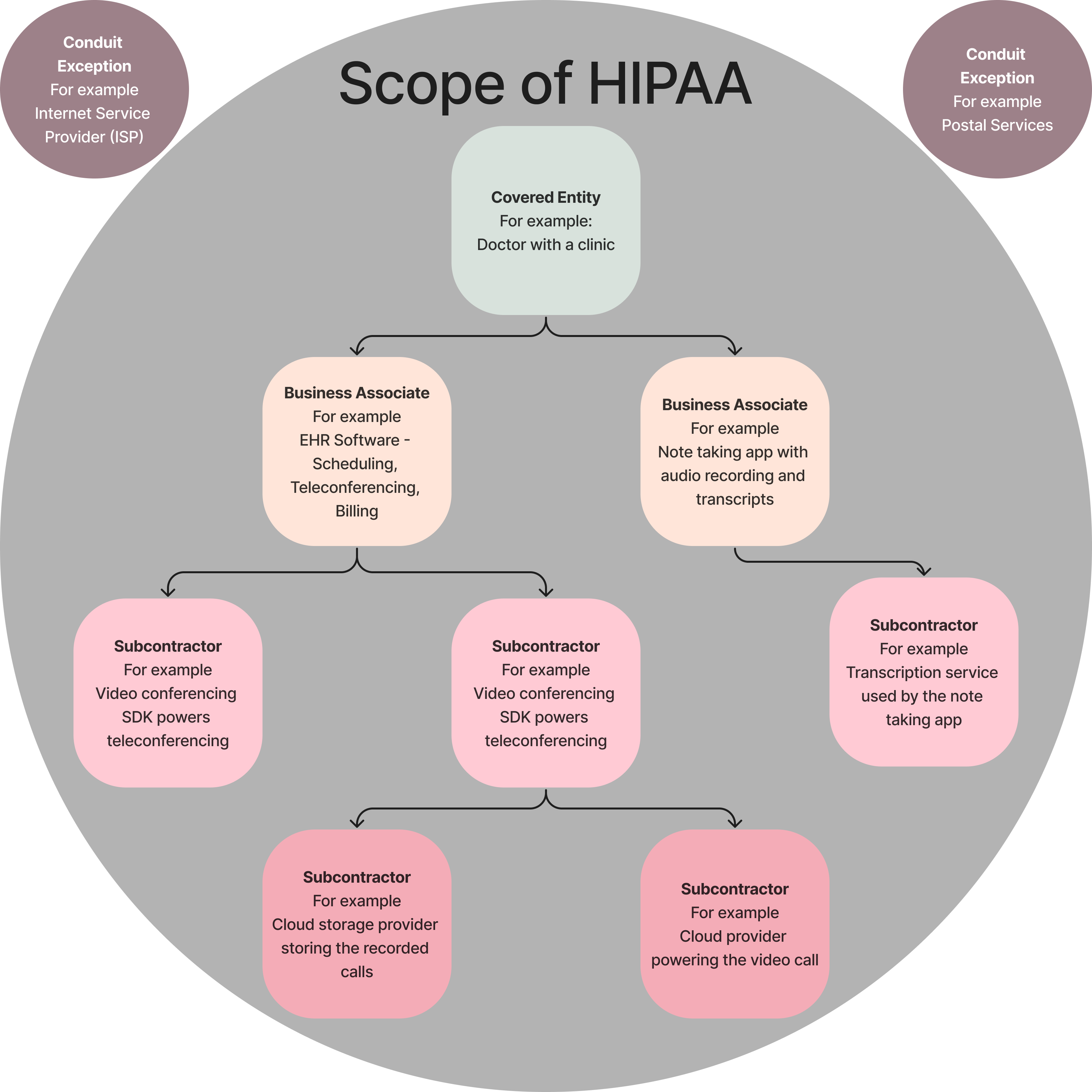
As we will see shortly, HIPAA applies to every one of these entities, and all of them are required to get into a HIPAA agreement with their respective business associates. More on the agreement later but there is one kind of entity in this which is not required to enter into an agreement.
There is an interesting exception within HIPAA called the ‘Conduit exception’ which excludes certain entities from being classified as Business Associates. Not all entities that come into contact with PHI are considered Business Associates. The conduit exception applies to organizations that act merely as conduits for the transport of PHI and do not access or view the information other than on a transient or incidental basis as necessary to perform the transportation service. Postal services or ISPs fall in this category.
The key guiding principles to understanding HIPAA
There are 3 key rules to understanding HIPAA. They apply to covered entities or their business associates who have created, received, maintained, or transmitted any PHI.
-
This rule is a cornerstone in protecting the privacy of individuals' medical records and other personal health information while allowing the flow of health data needed to provide and promote high-quality health care.
- Protect PHI (Protected Health Information) - The Privacy Rule protects all "individually identifiable health information" held or transmitted by covered entities. PHI could consist of medical records, recordings, transcripts, billing information, or any other information that could identify a patient and their associated health conditions.
- Minimum Necessary Standard - The rule requires that only the minimum necessary information be used or disclosed that is required for the purpose of the treatment.
- Patient Rights Over Their Information - Patients have rights over their health information, including the right to examine and obtain a copy of their health records and to request corrections.
- Restrictions on Certain Disclosures: The rule places restrictions on the use and disclosure of PHI for marketing, sales, and other purposes without explicit patient authorization.
-
This rule requires applicable entities to put in administrative, physical, and technical safeguards to protect from unauthorized access, breaches, and transmission security. This is to ensure the confidentiality, integrity, and availability of that information.
- Administrative safeguards would include policies on security officials, risk assessment and mitigation, workforce training, and information access management.
- Physical safeguards include policies and controls to protect data in case of environmental hazards and physical unauthorized intrusions. This could include device and media control of the workforce, security, and fail safes in case of possible breaches (like getting the device stolen).
- Technical safeguards include policies on access controls, audit controls and trails, and integrity controls (improper alteration or destruction.
- Risk analysis, monitoring, and periodic review along with having a policy on contingency planning is an important part of this rule.
-
Breach Notification Rule - In case of unsanctioned access or breach of ePHI, the covered entities, and their business associates are required to notify all the affected parties, HHS, and in some cases, media if the breach is big enough (affecting more than 500 people). This notification usually also includes mitigation measures that have been taken already and additionally, need to be taken by the affected parties to safeguard themselves from further harm and breaches. This notification must be released within 60 days of the breach.
In addition to these, we also have two more recent additions to these rules which are an extension;
- Enforcement Rule: Specifically, this rule gives the Office for Civil Rights (OCR) within the US Dept. HHS to conduct investigations and compliance reviews of covered entities as well as their business associates. This lays down when can these reviews take place, the method of complaint, categories of violations and associated penalties, and redressal mechanisms.
- Omnibus rule: These are a set of rules introduced to extend HIPAA’s reach and increase overall accountability for handling confidential data.
- Previously, business associates weren’t directly liable under HIPAA but this ruling directly makes them accountable.
- Previously, notification was required if the breach posed a "significant risk of harm" to the individual. The Omnibus Rule changed this to a presumption that any impermissible use or disclosure of protected health information (PHI) is a breach unless the covered entity or business associate demonstrates that there is a low probability that the PHI has been compromised.
Each rule under HIPAA not only details the responsibilities of the involved parties but also defines the hefty penalties that come along with their breach. Surprise assessments and security checks by the Office of Civil Rights (OCR) are a common occurrence and the fines can range from a couple hundred to millions of dollars. But the penalties aren’t limited to civil monetary fines, criminal proceedings can also be initiated which can have jail terms of up to 10 years in cases of negligence with malicious intent.
There is no official certification body for HIPAA. So the involved parties must make sure they are HIPAA compliant. To ensure that, most entities dealing with and exchanging sensitive health information enter into an agreement. These agreements are called Business Associate Agreements or BAAs.
What’s the significance of a BAA?
To outline the ways that a business associate complies with HIPAA, a Business Associate Agreement (BAA), covers the responsibilities and risks that the business associate is taking on. A BAA is a contract between a HIPAA-covered entity and HIPAA business associates.
This agreement outlines how both parties are practicing compliance. BAAs include:
- The services provided by the business associate.
- Types of data they are interacting with and details on permitted usage of the PHI by the business associates
- Responsibilities of the mentioned parties to comply with HIPAA
- Compliance duties as guided by HIPAA privacy, security and breach notification rules
- Termination and indemnification points
Ultimately, a business associate agreement (BAA) is mandated in order to meet HIPAA requirements and ensure that data security standards are upheld and that data is stored and used appropriately. But how can a covered entity be sure that its data is completely safe and that proper accountability measures have been taken?
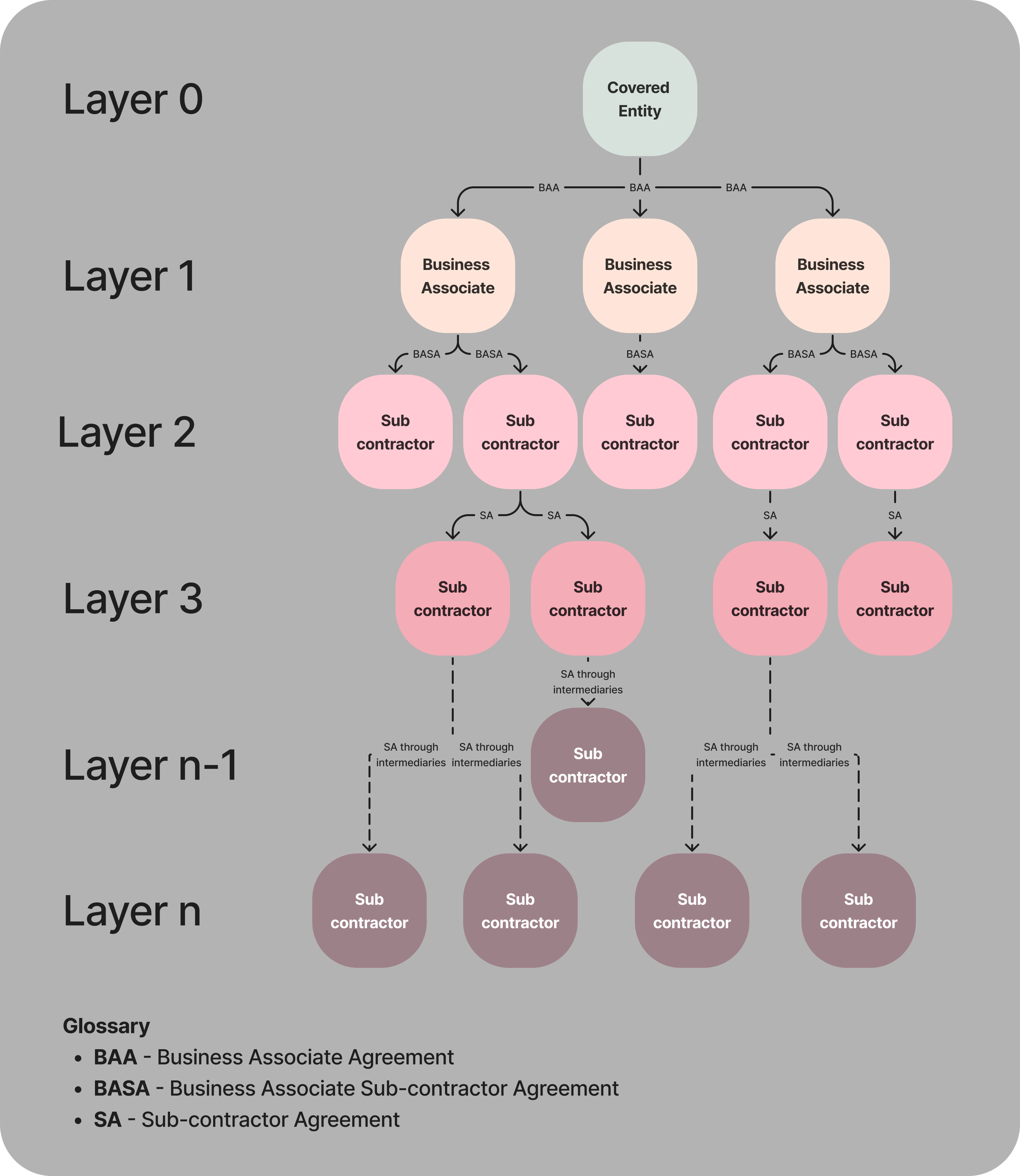
Each entity needs to sign a contract with the parties it is associated with in the layer above (providing services to) and below (getting services from) to self-regulate themselves. [See the chart above]
In cases where Business Associates themselves are using certain services that might access PHI, they are required to sign a BAA with the said subcontractor. Business Associate Sub-contractor Agreement (BASA) and SA (Sub-contractor Agreement) are just another form of BAA, but just between layers that are not directly interacting with a covered entity yet still receiving their PHI data in some form. But there are cases where BAA isn’t necessary. We have talked about it already - the conduit exception.
Here’s a model BAA provided by HHS for your reference.
HIPAA in Tech
HIPAA isn’t easy to implement. A lot of vendors will claim they’re HIPAA compliant, which might be true, but they may very well put the onus of integration of their service along with implementing the HIPAA guidelines on you. It is very important to understand how any of your potential business associates have implemented HIPAA compliance within their systems. We compiled a couple of questions that can help you get started with evaluating a service’s compliance level. These are broad questions with some specific details related to telehealth.
- Can you detail the types of Protected Health Information (PHI) your service encounters? How is this information processed, stored, and ultimately disposed of?
- What specific uses do you have for the PHI you collect? Please provide examples of how this information is utilized within your service.
- Regarding the electronic PHI (ePHI) generated by your service, could you explain how it is created, where it is stored, and the lifecycle of this data?
- Please elaborate on the encryption methods used for securing media and ePHI both in transit and at rest. Additionally, specify the retention periods for data stored in your databases.
- Do you have appropriate safeguards to protect the PHI that you’ve collected?
- What are administrative, physical, and technical safeguards put in place?
- Do you have access controls and audit trails within your critical services?
- For any subcontractors or third-party services you engage with, who might have access to PHI, do you establish Business Associate Agreements (BAAs)? How do you ensure their compliance with HIPAA? What are these services?
- Could you describe your data retention and deletion policies, especially as they pertain to PHI? How do you ensure that data is securely deleted?
- Besides HIPAA, are you compliant with any other data protection regulations or do you hold any certifications that impact your data handling practices (e.g., SOC 2, GDPR)?
- Where is the data physically stored? Please specify the regions or countries where our data will be hosted.
- In the event of a data breach, what are your policies for notifying affected parties and regulatory bodies? What steps are taken to mitigate the damage?
- What are the associated costs of enabling HIPAA compliance for our account and what is it going to cost us?
Wrapping up this primer on HIPAA compliance, it's clear that dealing with its complexities can be quite the task. But don't let the nitty-gritty of implementing these standards scare you off from using the services you need. It's really important to get a good grip on HIPAA – it helps you understand what's needed to make your systems compliant.
Here at 100ms, we've tackled the tough parts of HIPAA compliance so your integration is smooth and straightforward. We go the extra mile by turning away any PHI that's sent to us by mistake and setting up strong protections for the PHI that we do handle. If you're curious about how we've made HIPAA compliance a seamless part of what we offer, make sure that you’re subscribed to our blog and newsletter.
Basics
Related articles
See all articles