Home
/ Blog /
SIP Protocol - Everything You Need To KnowSIP Protocol - Everything You Need To Know
November 14, 20235 min read
Share
Definition
SIP is a signaling protocol used for initiating, maintaining, modifying, and terminating real-time sessions that involve video, voice, messaging, and other communications applications and services between two or more endpoints on IP networks.
Developed by the Internet Engineering Task Force (IETF), SIP is a crucial component in the Internet telephony and VoIP (Voice over Internet Protocol) landscape, providing the mechanisms for setting up and controlling communication sessions. It is characterized by its scalability, flexibility, and its ability to integrate seamlessly with existing internet protocols and services. SIP functions independently of the underlying transport layer and can be used with several transport protocols such as UDP, TCP, and SCTP.
What does it really mean?
Setting up the Event (Call Initiation)
When you want to start a call or video conference (akin to organizing an event), SIP acts like an event coordinator who sends out invitations (call requests). It contacts the intended recipient (another phone or computer) and asks if they are available and ready to join the event (the communication session).
Negotiating the Details (Call Setup)
Once the recipient agrees to join the call, SIP helps negotiate the details, much like an event planner deciding on the venue, time, and other arrangements. In the digital world, this involves determining the best format and path for the communication, such as video, audio, or messaging, and the technical parameters for these media types.
Running the Event (Call Management)
During the call, SIP oversees the event, ensuring everything runs smoothly. It can modify the call by adding more participants or changing the communication medium (like shifting from a voice call to a video conference), much like how an event coordinator might adjust seating arrangements or manage unexpected changes during an event.
Concluding the Event (Call Termination)
When the call or session is over, SIP steps in to wrap things up, just as an event planner would signal the end of an event, oversee the departure of guests, and handle any closing details. SIP closes the communication session and ensures all resources used for the call are properly released.
History of SIP
What was used before SIP?
- ISDN and PSTN: Before SIP, telecommunication was predominantly based on the Public Switched Telephone Network (PSTN) and Integrated Services Digital Network (ISDN). These were circuit-switched networks, designed primarily for voice communications.
- H.323 Protocol: In the early days of internet-based telecommunication, H.323 was a prominent protocol. Developed by the International Telecommunication Union (ITU), it was designed for multimedia communication over networks that do not provide a guaranteed quality of service.
- Proprietary Protocols: Various proprietary protocols existed, each limited to specific hardware or software platforms, which hindered interoperability and widespread adoption.
What challenges did it face?
- Complexity: H.323, while robust, was complex and difficult to implement and manage. It required a significant amount of resources, which was a barrier to widespread usage, especially for smaller organizations and individual users.
- Lack of Flexibility: The earlier protocols, including both H.323 and PSTN/ISDN-based systems, lacked flexibility. They were not designed with the modern, dynamic nature of Internet communications in mind, making them less suited for rapidly evolving digital communication needs.
- Interoperability Issues: The existence of various proprietary protocols led to interoperability issues. Devices and systems using different protocols could not easily communicate with each other, limiting the scope and reach of digital communication.
How SIP is solving it?
- Simplicity and Scalability: SIP was designed to be simpler and more scalable than its predecessors like H.323. Its simplicity allowed for easier implementation and management, making it more accessible for a broader range of applications and users.
- Interoperability: SIP was developed as an open standard by the Internet Engineering Task Force (IETF). This openness ensured that it could work across different networks and devices, fostering interoperability and encouraging widespread adoption.
- Flexibility: SIP was designed with the internet in mind, meaning it could easily integrate with various internet services and protocols. This flexibility made it well-suited for the diverse range of communication needs in the modern digital era, such as VoIP, video conferencing, instant messaging, and presence information.
- Internet-Centric Approach: Unlike H.323, which was more telephony-centric, SIP embraced an internet-centric approach. This made it more adaptable to the evolving landscape of Internet communications, including mobile and cloud-based applications.
Core SIP Operations
Request-Response Mechanism
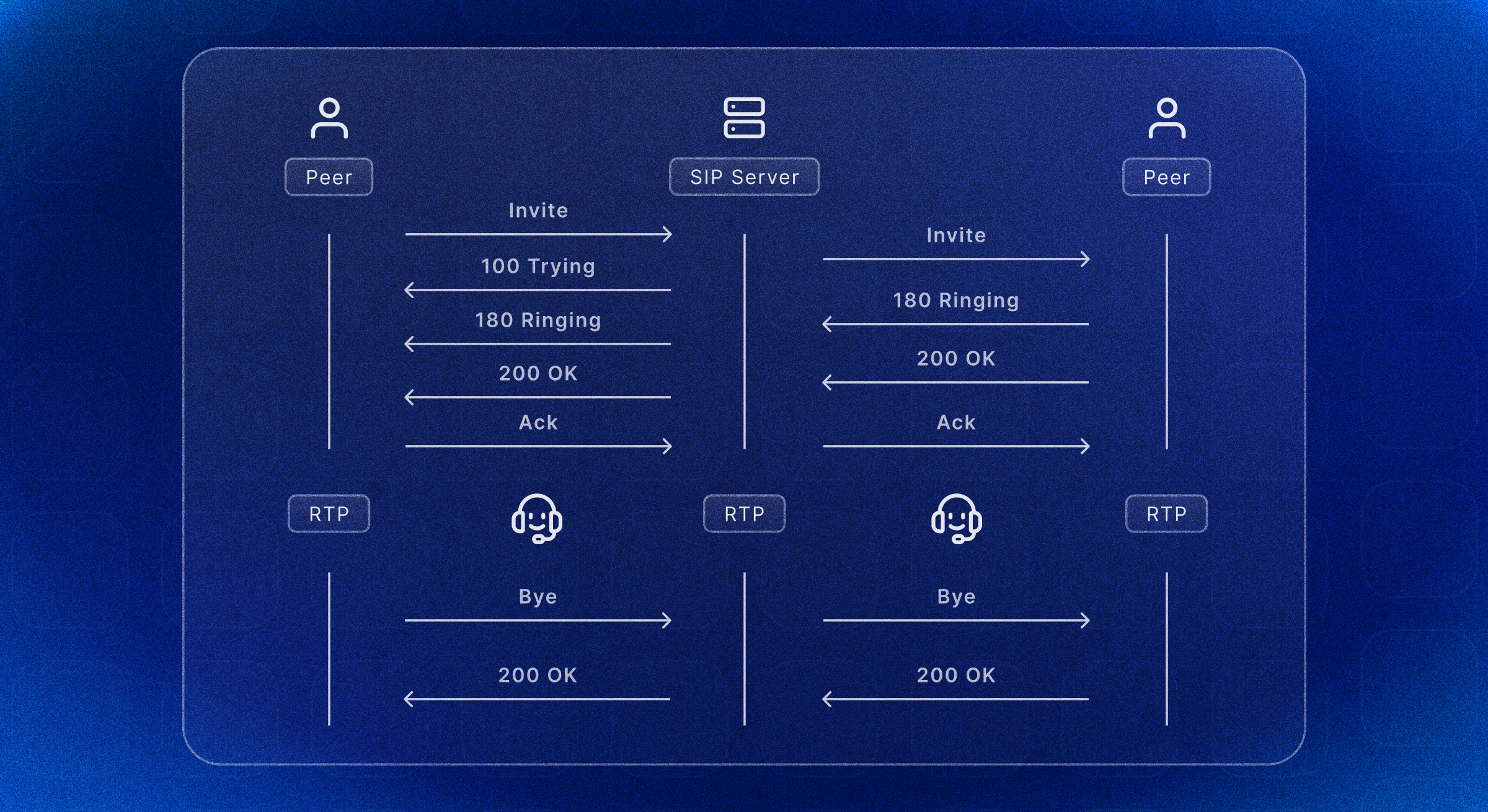
SIP operates on a request-response model similar to HTTP. It uses methods like INVITE, ACK, BYE, CANCEL, REGISTER, and OPTIONS, each serving a specific purpose in establishing and managing sessions. Responses are categorized into six classes, ranging from Provisional (1xx) to Global Failure (6xx), indicating the status of the request.
INVITE Transaction
The INVITE request initiates a session. It includes a session description, typically using SDP (Session Description Protocol), which specifies the media capabilities (like codecs) and network addresses for media streams. Upon receiving an INVITE, the recipient responds with a 1xx (Provisional) response, followed by a 2xx (Successful) or error response. The 2xx response contains the recipient's media capabilities and choices. The ACK method finalizes this transaction, acknowledging the receipt of the final response to an INVITE request.
Session Establishment and Negotiation
Media negotiation is handled by SDP carried within SIP messages. SDP defines parameters like media type (audio, video), transport protocols (RTP/RTCP), and codec information. SIP doesn't transport media itself but uses RTP (Real-time Transport Protocol) for media streaming, with RTCP (Real-time Transport Control Protocol) providing out-of-band statistics and control information.
Session Modification and Termination
An existing session can be modified using a new INVITE request (re-INVITE), which may alter the session parameters (e.g., adding video to an audio call). The BYE method terminates a session, and both parties must acknowledge this termination.
Advanced Features and Mechanisms
SIP Proxies and Registrars
SIP utilizes proxy servers to assist in session establishment and routing requests to the recipient's current location. Registrars are used to register users' current locations, aiding in SIP routing.
SIP Transactions and Dialogs
A SIP transaction consists of a request and its associated responses. Transactions are atomic and manage the signaling between two SIP endpoints. A dialog is a peer-to-peer SIP relationship between two UAs (User Agents) that persists for some time. It's established by INVITE requests and terminated by BYE requests.
Security Mechanisms
SIP employs various security mechanisms, including SIP over TLS for encryption, and S/MIME for message integrity and confidentiality. Authentication is typically handled via HTTP Digest, although newer methods like OAuth are being integrated.
NAT Traversal
SIP faces challenges with NAT (Network Address Translation). Solutions include STUN (Simple Traversal of UDP over NATs), TURN (Traversal Using Relays around NAT), and ICE (Interactive Connectivity Establishment) protocols.
Integration with Other Protocols
SIP is often integrated with other protocols like Diameter for AAA (Authentication, Authorization, and Accounting) and WebSocket for SIP as part of WebRTC for real-time communication in web browsers.
Frequently Asked Questions
Does SIP use TCP or UDP?
SIP (Session Initiation Protocol) can use both TCP (Transmission Control Protocol) and UDP (User Datagram Protocol) for signaling in VoIP and other communication systems. The choice between TCP and UDP depends on the specific requirements of the network and application.
Is SIP traffic encrypted?
SIP traffic is not encrypted by default, but it can be secured using TLS (Transport Layer Security) to provide encryption for SIP signaling. This ensures secure and private communication sessions in VoIP and other SIP-based communications.
What is an SIP firewall?
An SIP firewall is a specialized network security device designed to protect SIP-based communication systems, like VoIP. It monitors, filters, and controls SIP traffic to defend against threats such as fraud, eavesdropping, and denial-of-service attacks, ensuring secure and reliable communication.
References
https://en.wikipedia.org/wiki/Session_Initiation_Protocol https://www.tutorialspoint.com/session_initiation_protocol/session_initiation_protocol_introduction.htm https://www.geeksforgeeks.org/session-initiation-protocol/ https://datatracker.ietf.org/doc/html/rfc3261
Glossary
Related articles
See all articles